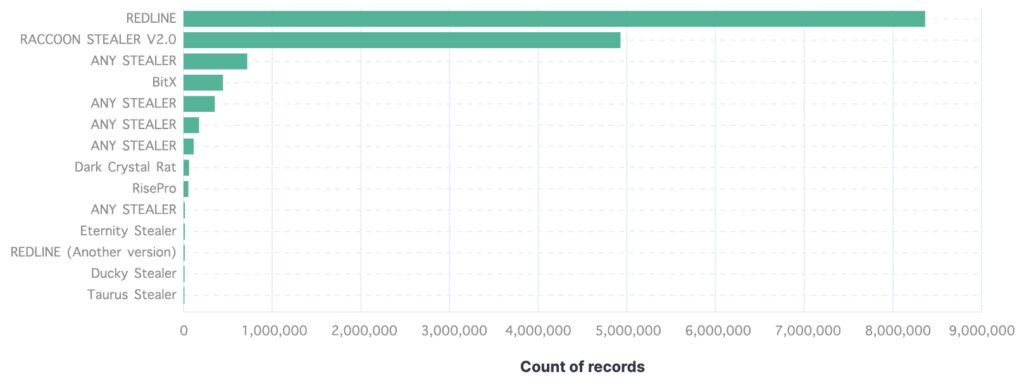
Unmasking the Giants: An In-Depth Analysis of the Most Prolific Stealers in Cyberspace
In the vast and murky world of cyber threats, Stealers – a type of malware designed to exfiltrate sensitive data from infected systems – have carved out a notorious reputation. As a security analyst, I’ve been tracking the activities of these digital predators through my service, “MyDataIsLeak”. Today, I’m sharing an analysis of the most prevalent Stealers, based on the volume of records they’ve compromised.
Let’s dive into the specifics:
- REDLINE takes the lead, having amassed a staggering 8.36 million records. This accounts for approximately 52.2% of the total records stolen by the Stealers on this list.
- The second spot is claimed by RACCOON STEALER V2.0, responsible for the theft of 4.92 million records, which equates to roughly 30.7% of the total.
- ANY STEALER variants, custom-made by hackers without a public selling page or a specific name, collectively rank third. They’ve pilfered 718,000 records, making up about 4.5% of the total.
- BitX follows closely, having compromised 445,000 records, or approximately 2.8% of the total.
5-8. Other variants of ANY STEALER have stolen 352,000, 175,000, and 114,000 records respectively, contributing to a combined total of 4.0%.
- Dark Crystal Rat has exfiltrated 62,600 records, accounting for about 0.4% of the total.
- RisePro has stolen 54,500 records, which is roughly 0.3% of the total.
- Another variant of ANY STEALER has compromised 15,200 records, making up about 0.1% of the total.
- Eternity Stealer has stolen 14,400 records, contributing to about 0.09% of the total.
- A different version of REDLINE has compromised 13,400 records, accounting for approximately 0.08% of the total.
- Ducky Stealer has exfiltrated 11,300 records, making up about 0.07% of the total.
- Lastly, Taurus Stealer has stolen 10,100 records, which equates to roughly 0.06% of the total.
In summary, the top two Stealers, REDLINE and RACCOON STEALER V2.0, are responsible for a whopping 82.9% of the total records stolen, highlighting their dominance in the Stealer landscape. The remaining Stealers, while individually less impactful, collectively contribute to a significant portion of the total records stolen, underscoring the broad and diverse threat landscape we face.
As we continue to navigate the digital age, understanding the scale and impact of these Stealers is crucial in developing effective countermeasures. Stay vigilant, stay informed, and most importantly, stay secure.