Achieving Effective Exposure Management: Insights from 500 Chief Information Security Officers

Recent findings from an extensive survey conducted by Pentera, which involved approximately 500 Chief Information Security Officers (CISOs) globally, highlight the progressive evolution of Exposure Management practices. However, notable disparities remain within the market that demand attention.
The modern attack surface is increasingly complex, covering a vast and dynamic range of environments. As enterprises transition towards cloud-native structures, incorporate numerous APIs, and introduce Internet of Things (IoT) and Operational Technology (OT) devices into their core operations, the potential vector for cyber threats expands significantly. Presently, the average enterprise manages around 75 security tools, with nearly half of the CISOs reporting a continual increase in their security infrastructure year over year.
This complexity does not deter adversaries; it fuels their efforts. Attackers exploit vulnerabilities opportunistically, targeting the weakest areas within a system. For security leaders, the challenge lies not in merely expanding coverage but in discerning where to concentrate efforts for optimal security. Identifying the most significant risks and where potential threats are concentrated becomes paramount.
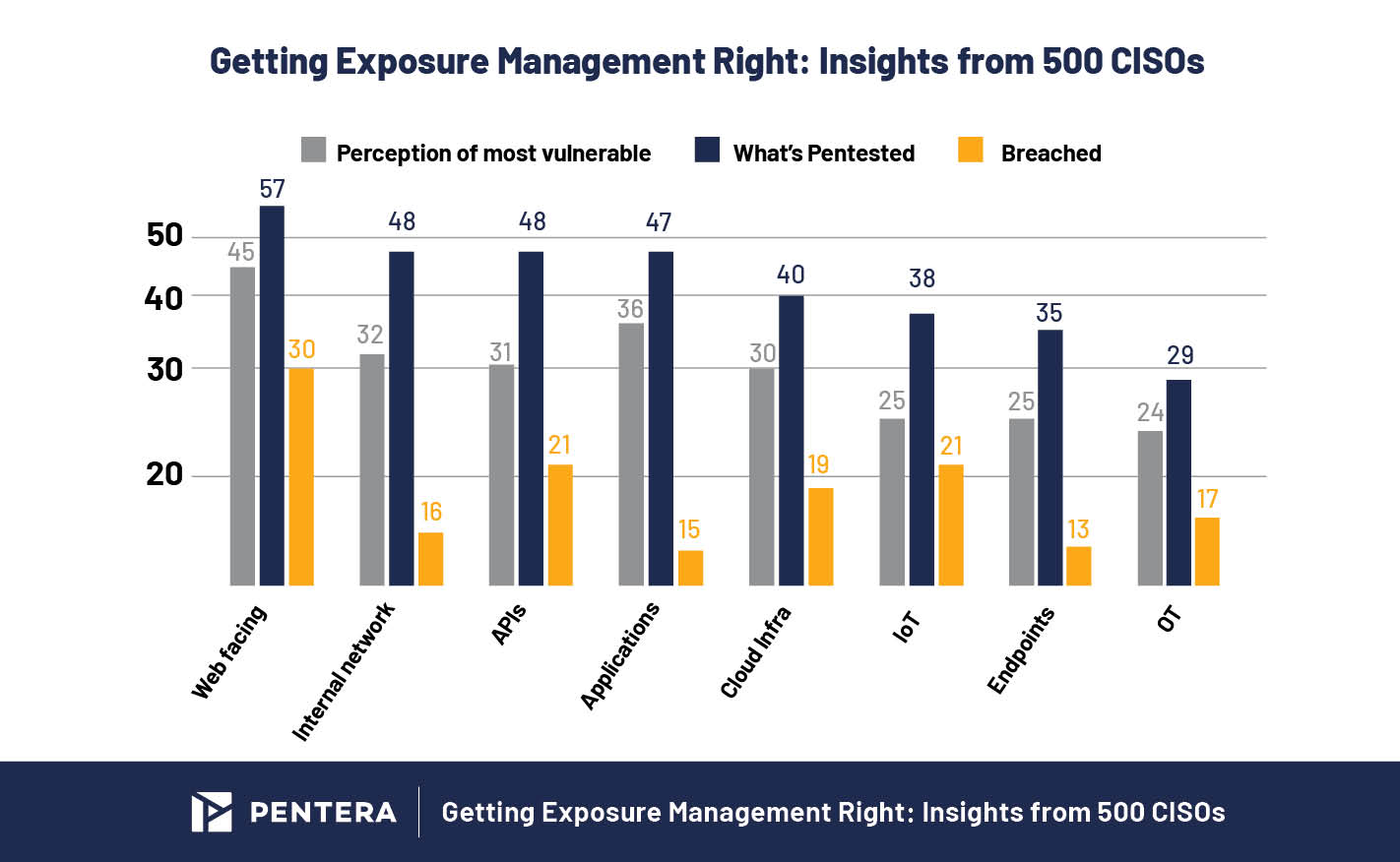
The latest report reveals vulnerabilities across diverse attack surfaces, ranging from cloud infrastructure and web-facing assets to APIs, endpoints, and IoT systems. CISOs were queried regarding their perceptions of risk, directing pentesting efforts, and areas where breaches were most frequent. The insights gleaned from this evaluation empower security teams to refine their focus, enhance testing strategies, and expedite the closure of the most precarious exposures.
The Little Realized Truth about Exposure Management
Even in highly effective exposure management programs, breaches can occur. However, with an evolved security framework, it becomes evident that a breach does not always equate to a compromise.
Consider an exposed asset: while it may be technically breached—potentially allowing an attacker to gain access—if that asset is not connected to sensitive data, critical operations, or essential services, the actual impact is likely to be minimal.
It is vital to understand that not all breaches carry the same weight. This represents a foundational shift in mindset that effective exposure management promotes.
In contrast to conventional vulnerability management, which often fixates on CVEs based on severity or age, exposure management adopts a strategic perspective. It evaluates both exploitability and impact to ascertain which vulnerabilities are genuinely consequential. This dual approach enables teams to cut through distractions and hone in on those exposures that pose the most significant risk of substantial compromise.
The State of Pentesting report corroborates this perspective; despite nearly 67% of enterprises reporting a breach within the past two years, only 36% experienced operational downtime, 30% encountered data exposure, and 28% faced financial ramifications. This indicates that a considerable portion of “breaches” resulted in minimal operational consequences. The objective is not to eradicate all breaches but to mitigate those that can inflict financial or operational damage.
Web-Facing Assets – Still the Weakest Link
Exposure management fundamentally aligns remediation efforts with risk, and web-facing assets exemplify this principle.
Data indicates that web-facing assets are perceived as the most susceptible, with 45% identified as vulnerable, 57% subjected to testing, and 30% having experienced breaches.
This prioritization reflects positively on security teams, as they recognize external assets as both significant targets and accessible threats, consequently directing their pentesting resources effectively.
Despite this attention, the reality is that attackers continue to breach these defenses.
The inherent risk of web-facing assets lies in their design; systems such as DNS, web portals, and login pages are intentionally open and reachable. Their exposed nature renders them susceptible, particularly when misconfigurations, exposed services, or open ports are unchecked and not supplemented by security measures like multi-factor authentication.
Nonetheless, such breaches do not necessarily equate to failure.
Should adversaries compromise a public asset but encounter barriers that prevent access to sensitive data or critical systems, the breach’s actual impact may be negligible. Therefore, the focus of exposure management shifts from merely reducing breach occurrences to minimizing the repercussions of breaches that do take place.
Internal Networks, Endpoints, and Applications – A Contained Front
Organizations are demonstrating effective practices with their internal networks, endpoints, and applications, which are subjected to extensive testing (48%) and perceived as vulnerable (32%), with a low breach rate (16%).
These critical systems house sensitive information and operational continuity, showcasing reduced breach rates: 16% for internal networks, 13% for endpoints, and 15% for applications—indicative of a beneficial focus and investment in security measures.
The priority reflects a conscious effort to bolster security protocols surrounding systems integral to operations. By adopting robust verification and penetration testing services within these environments, organizations can prioritize based on potential impact, ensuring defenses are both validated and reinforced under scrutiny.
API Risk – Shows Gap Between Perception and Reality
APIs represent the convergence of business logic and backend operations, proving essential yet often overlooked, as survey data suggests that their vulnerability may be underestimated by security teams.
Although APIs are tested at comparable rates to internal networks (48%), they exhibit a heightened breach rate of 21%, exceeding the 16% seen in internal networks. This discrepancy indicates a possible misalignment in perceived versus actual risk.
The challenge with APIs lies in their inherent complexity; they are dynamic and challenging to inventory. Their attack surface encompasses not only ports and endpoints but also logic flaws, authentication issues, and misconfigured integrations that standard scanning methods may fail to identify.
Furthermore, APIs frequently connect diverse systems, bridging the gap between cloud services, third-party applications, mobile platforms, and internal databases. This interconnectedness makes them prime candidates for lateral movement or data exfiltration, while limited visibility enhances their appeal to attackers.
Addressing this gap necessitates an advancement in testing methodologies, emphasizing both the frequency and thoroughness of assessments. Continuous, adversarial API testing is crucial for uncovering the integration vulnerabilities that conventional approaches overlook.
Exposure Management Shows Encouraging Signs of Alignment
The 2025 State of Pentesting report reinforces the longstanding understanding that a closer alignment with business risk enhances execution.
Notable alignment has emerged between perceived risk, pentesting activities, and actual breaches, signaling maturation in exposure management practices as organizations narrow the divide between perceived and real threats.
The principal goal of exposure management is not to extinguish every breach but rather to thwart those that bear significance. By utilizing data-driven prioritization alongside continual validation, security teams can concentrate on genuine exposures rather than theoretical risks, ensuring that sensitive assets remain fortified against potential threats.
To gain deeper insights into how leading organizations are successfully implementing their Exposure Management strategies, participating in the Xposure National Exposure Management vSummit is highly recommended.

