Exploitation of Google Apps Script by Malicious Actors in Sophisticated Evasion Tactics for Phishing Attacks
Threat actors are exploiting the Google Apps Script development platform to facilitate sophisticated phishing attacks that mimic legitimate services and extract login credentials from unsuspecting users.
Recent observations by security experts at Cofense have identified a method where attackers deploy fraudulent login interfaces designed to closely resemble authentic login pages. These phishing attempts typically begin with an email appearing to be an invoice or a tax notice, containing a link to a phishing webpage hosted on the Google Apps Script platform, which is integrated with various Google products.
Hosting phishing pages within Google’s trusted environment significantly enhances the illusion of legitimacy, increasing the likelihood of deceiving recipients into disclosing sensitive information. Cofense notes, “By utilizing this trusted platform, attackers provide a false sense of security, facilitating the capture of sensitive user data.”
Exploitation of Legitimate Services
Google Apps Script is a cloud-based scripting platform that enables users to automate tasks and expand functionalities within Google Workspace products such as Sheets, Docs, Drive, Gmail, and Calendar. The scripts operate on a trusted domain under “script.google.com,” typically considered safe by most security solutions.
In practice, attackers create Google Apps Scripts that generate counterfeit login pages to intercept credentials input by victims. The collected data is transmitted to the attackers’ servers through covert requests.
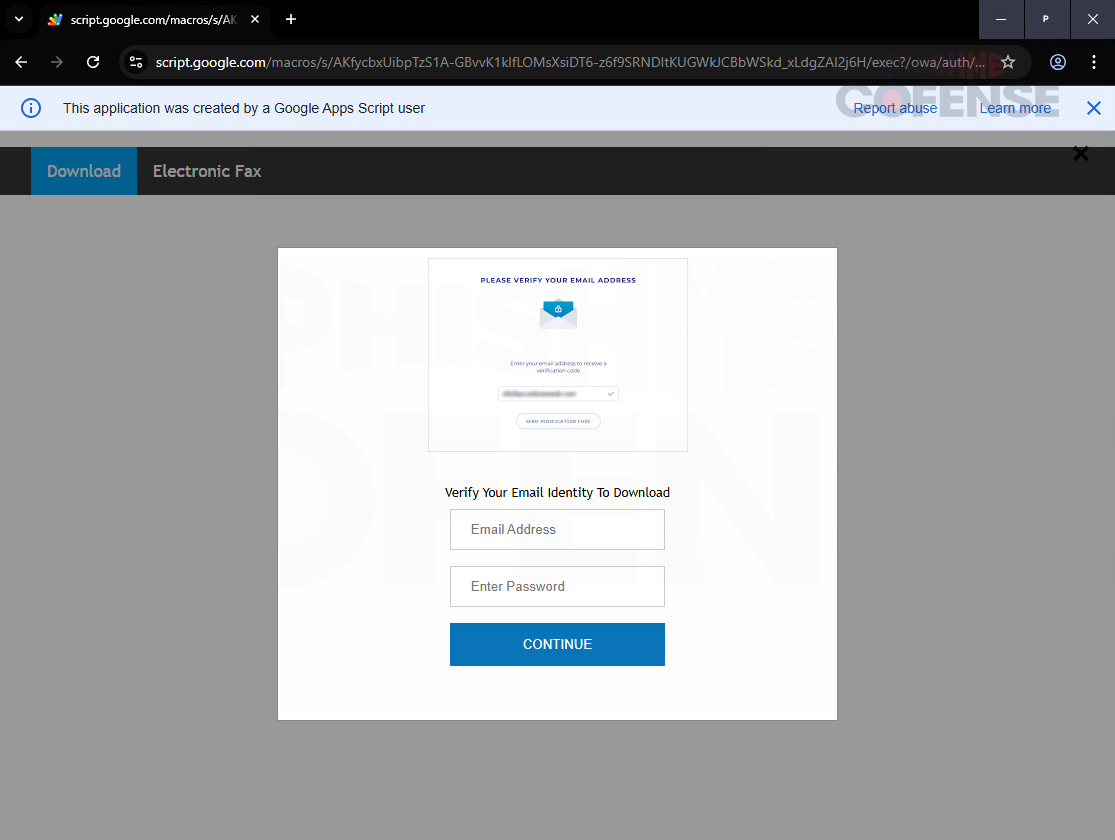
Due to the capability of anyone with a Google account to publish scripts as public web applications under a Google domain, threat actors can efficiently disseminate these phishing links through emails that bypass security flags. The phishing email engages recipients with payment-related themes, redirecting them to the harmful Google-hosted pages.

Once victims provide their credentials, they are redirected to the legitimate service that the attackers have impersonated, thereby minimizing suspicion and affording attackers time to exploit the compromised information.
The sophistication of this tactic illustrates a new frontier in phishing, as malicious actors increasingly seek to leverage legitimate platforms like Google Apps Script for greater evasion effectiveness and operational agility. This method allows attackers to adjust their scripts on-the-fly without requiring new links, facilitating a smooth transition to different types of bait without considerable effort.
To mitigate risks from such phishing attempts, organizations should implement stringent email security protocols that rigorously evaluate links to cloud services. Blocking access to Google Apps Script URLs or flagging them as potentially hazardous is recommended as a proactive defense measure.
Efforts to communicate with Google regarding potential countermeasures in response to these security findings have been initiated; however, no response has been received at this time.

